This Amazing Website Helps You Detect if The Latest Viral Photo Was Faked

If you’ve ever seen a crazy photo on the internet and wondered whether it’s even real, you might be excited to find that yes, there’s an app analysis tool for that.
The FotoForensics website, developed by computer scientist Neal Krawetz, has been around since 2012 – which can make it feel a bit arcane by modern web design standards.
But it’s actually pretty easy to use, as we’re about to show you.
Before we start, you need to be warned that FotoForensics doesn’t provide you with definitive yes/no type answers – but if you’re willing to spend a few minutes to familiarise yourself with its tools, you’ll have a great new first mate in your quest to navigate the sea of fake news.
“It works like a microscope – by highlighting artifacts and details that the human eye may not be able to identify,” Krawetz explains on the site.
The analysis process is pretty simple: you submit a photo to the site (either as an upload or just from a link), its algorithms crunch through it and spit out a result which you can interpret to come to your own conclusions.
The tricky part is understanding what you’re looking at when the results show up on your screen. As a test example, we took this green rubber ducky that melted minds on Twitter in July 2017.

While the original tweet by user @shiohitoshi has unfortunately been lost in the aether, there was no shortage of copies, so it was easy to download a high-resolution version someone had posted to their own Twitter (which, by the way, is not the ideal approach, but more on that later).
When you look at the photo of the blob, it actually looks pretty convincing. But we specifically wanted to see whether the face of the duck may have been digitally edited onto the blob to make it look like the duck had melted.
Here’s what we got:
 (FotoForensics)
(FotoForensics)
Of course, you were already warned that you’re not getting a ‘yes’ or a ‘no’ here, but what are we even looking at?
The most powerful part of the FotoForensics tool is the Error Level Analysis (ELA) algorithm, which “highlights differences in the JPEG compression rate” of the picture. In practice, this means that it can tell differences between edges, textures, and surfaces that could escape the naked eye.
The best way to understand the ELA tool is to do a practice round with some challenges Krawetz has helpfully put together for novice users.
Below is an ELA analysis from one of these tutorials: the ELA brightness of the fake floppy disk in Kim Jong Un’s hand indicates it’s not the item he was actually holding:
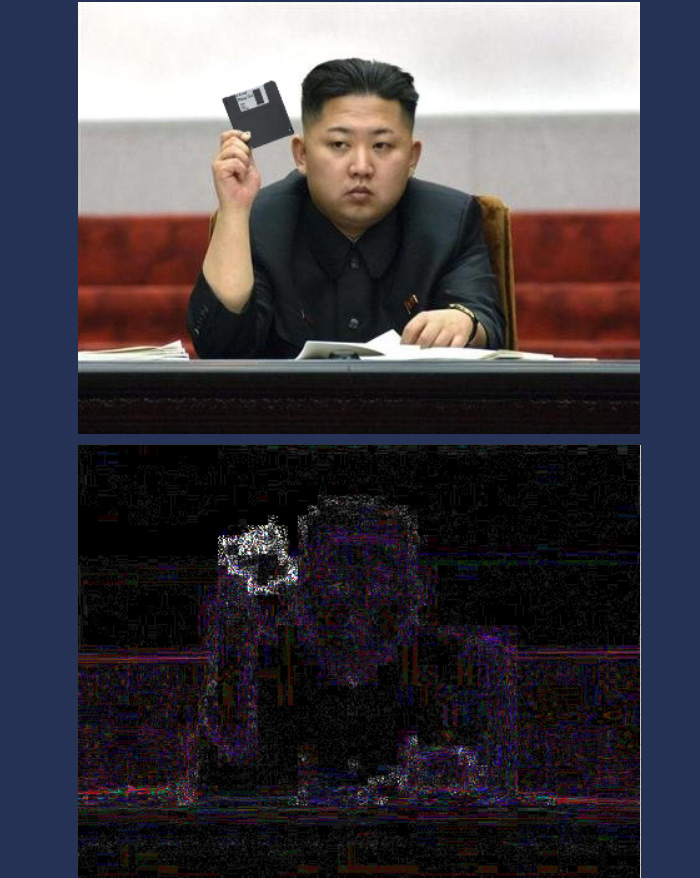 Example of ELA (FotoForensics)
Example of ELA (FotoForensics)
Okay, so if ELA can find bits of a picture that have been pasted into another picture, that molten duck blob with its uniform edges and surfaces suddenly looks a lot more convincing. Other reports have shown the duck blob was indeed real, so we have additional evidence to trust here, too.
In addition to ELA, FotoForensics also digs through the image metadata, which can provide crucial additional information on the file you’re investigating, such as whether it was edited in Adobe Photoshop, or came directly from a camera.
Wherever possible, you should try to get the original picture for analysis, because the more it’s kicked around the internet, the more compressed it’s going to be.
“A viral photo can quickly undergo dozens or hundreds of alterations,” the site states. “Each modification changes the image and makes evaluating the content more difficult.”
So, next time you’re faced with a compelling meme and feel like playing digital Sherlock Holmes (who doesn’t?), you can employ FotoForensics to help you. Before you start, make sure to have a go at the challenges, read the in-depth descriptions of all the tools, and familiarise yourself with common mistakes.
Just, maybe, don’t go overboard with your conclusions.
[“Source-sciencealert”]